Cloudflare for Individual Users
Last Updated: May 13, 2026
25+ Reasons We Love Cloudflare
Cloudflare can be an indispensable asset for your site and here are 25 awesome features that are enabled by default under their free plan:
- Brotli
- Standard level of Automatic Static Content Caching with instant cache purge
- Always Online (keeps the static portion of your site online when origin server is down)
- HTTP/2 and Opportunistic Encryption and SPDY
- IPv6 Compatibility
- Websockets
- IP Geolocation
- 10 free User Agent Blocking rules (helpful with preventing bad bots, spiders, and crawlers)
- Security level of Medium enabled with Challenge Passage (both configurable)
- Browser Integrity Check
- Free Origin Certificates (must be installed at your origin server)
- Analytics
- Under Attack Mode (available to enable but not enabled by default)
- Unlimited Bandwidth
- Unlimited Websites
- DDOS mitigation (unmetered)
- a globally load-balanced CDN
- Health checks every 60 seconds (Health checks ping origin server to determine if it is online)
- Universal SSL/TLS 1.2 and 1.3 Encryption with a 24 hour activation time that work on most modern browsers
- TLS Optimization
- DNSSEC (not enabled by default, but you have the option to enable)
- Free access to email support with a median response time of 13 hours
- Email Address Obfuscation (to prevent your email address from being harvested for spam lists)
- Server Side Excludes
- CNAME flattening at the root of your domain
You even have access to most of these features via a RESTful API! If you aren’t convinced yet, well check out some of the features discussed below that you have the option to enable under the free plan with no extra costs. These are features that you’ll want to consider enabling to get the most out of Cloudflare’s free plan. You can read more about each of these features inside the Cloudflare dashboard or via their documentation. But first, let’s discuss how to get Cloudflare enabled for your domain and then we can go through these settings together.
Enabling Cloudflare
Create a free account at Cloudflare.com by clicking ‘Sign Up.’ You can use the following URL to go directly to the Sign Up page for Cloudflare here:
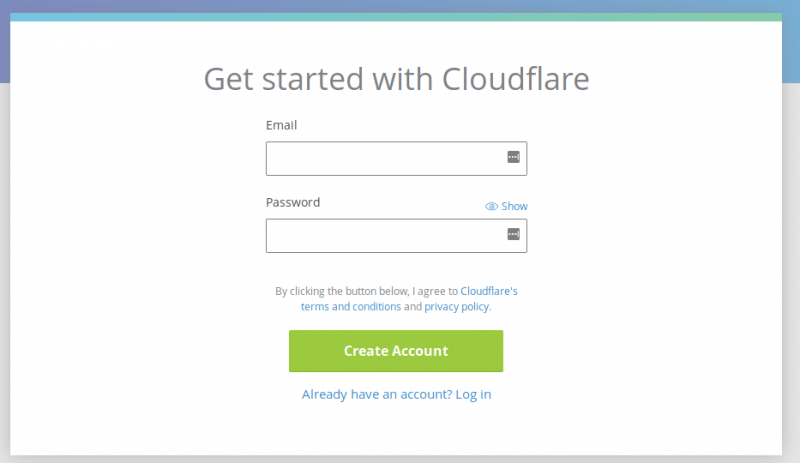
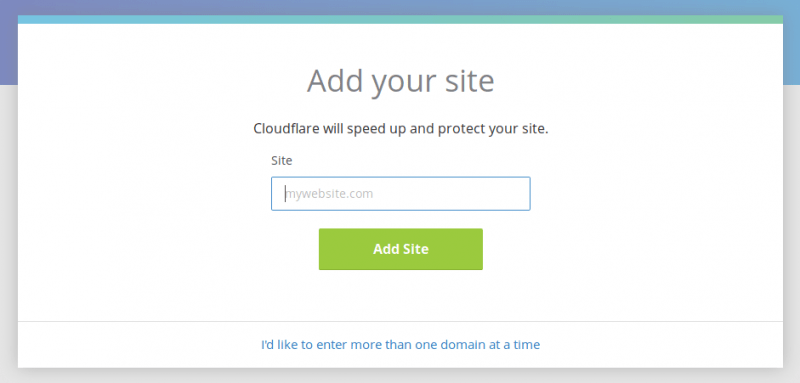
Click “Create Account” to create a free account if you do not already have a Cloudflare account. Enter the requested details, and then your site that you want to use with Cloudflare.
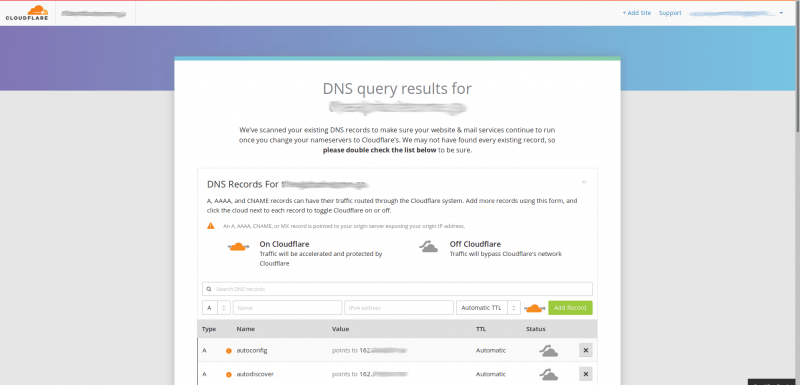
2) Allow Cloudflare to scan your DNS records. This process will take approximately 60 seconds to complete.
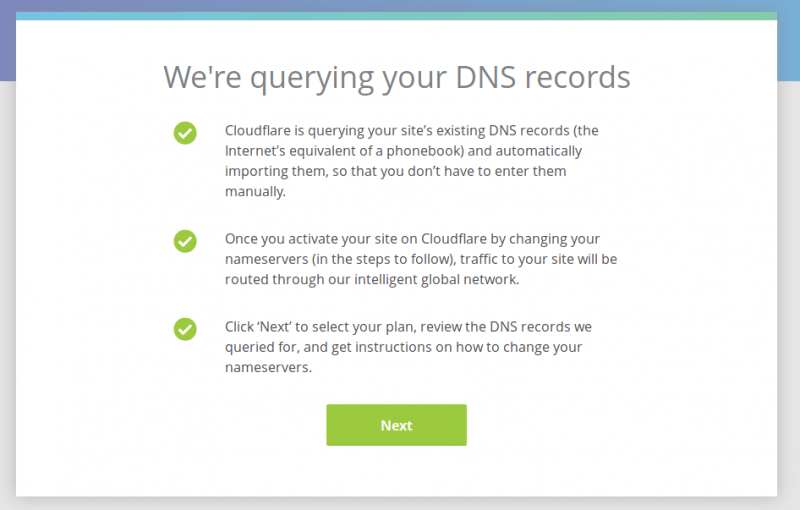
It is great if the domain is new and no DNS records exist for it yet. You can add them manually.
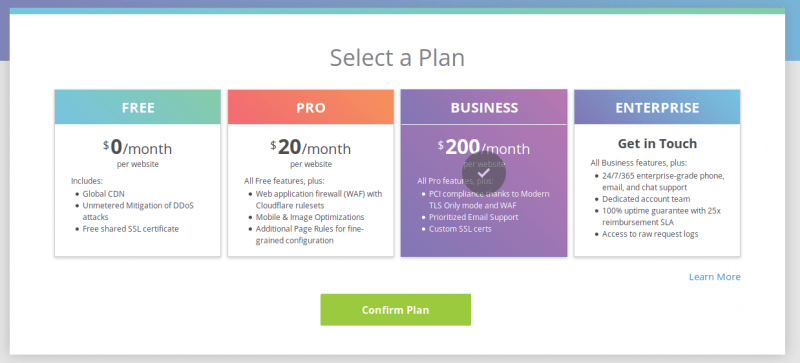
3) Select your plan and confirm your DNS results from the previous scan are correct.
If you have previously set up nameservers, you will find that Cloudflare scanned and found your records for you, though you should still check them to ensure that they are all there and correct:
If you are adding them manually instead, you will see something like this:
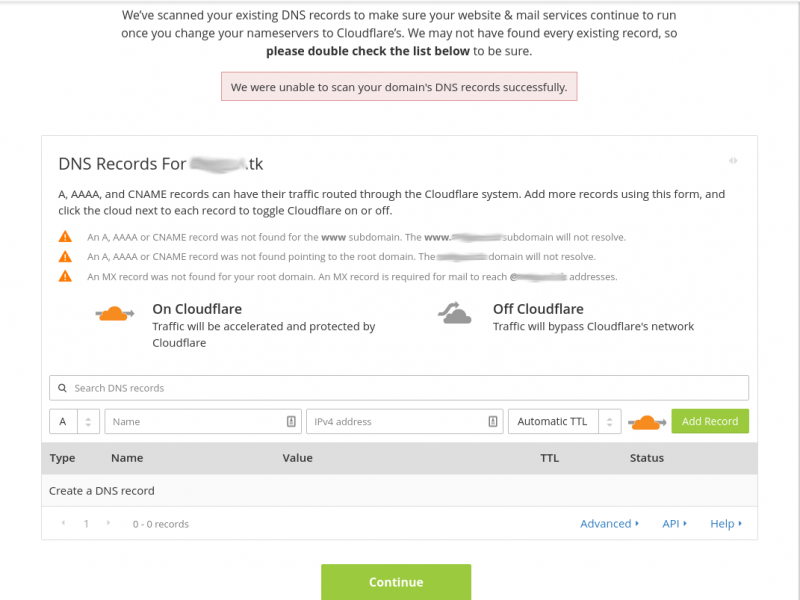
You can now proceed to enter your DNS records here to create your DNS zone file. At the minimum you will want to enter the following records:
- www CNAME domain
- @ A IP
- @ TXT “v=spf1 +a +mx ~all”
- @ MX MX record provided by your mailserver
Other records you may wish to include are as follows:
- Subdomain A records if you have, or will have subdomains
- a DKIM record
- a DMARC record
- a CNAME for the ‘mail’ subdomain
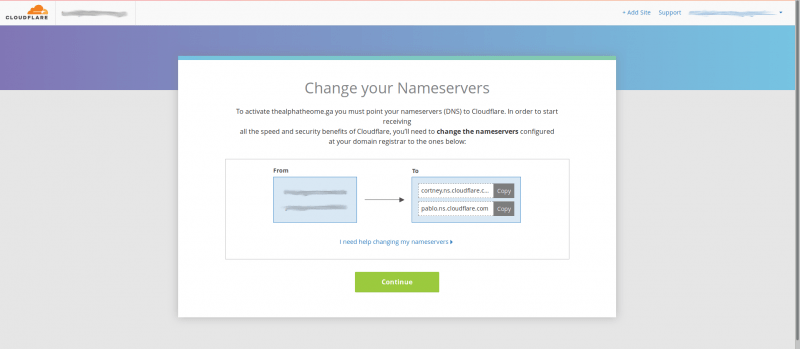
4) Get your Cloudflare nameservers and set these as the custom nameservers at your registrar. Cloudflare has an amazing resource for this. Changing your domain nameservers to Cloudflare
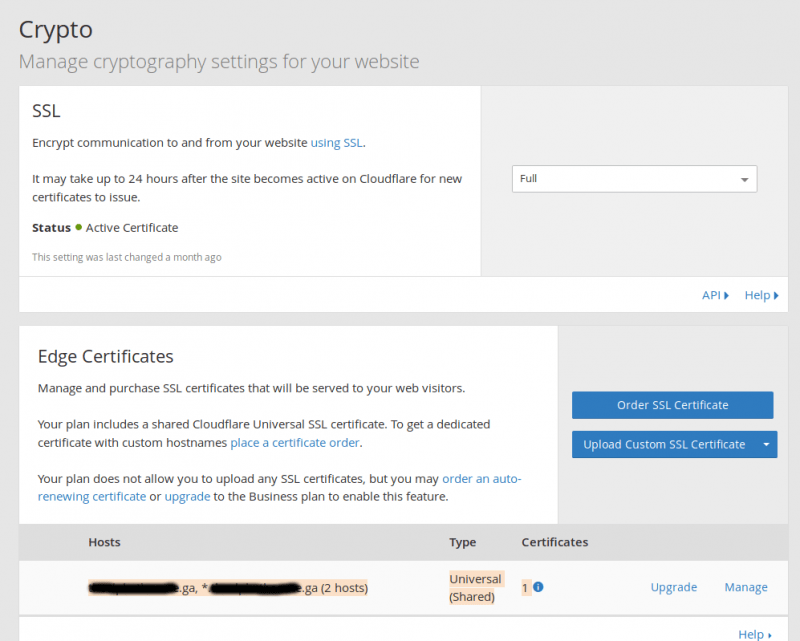
5) Check under Edge Certificates under the Crypto tab to see if your Universal SSL is ready. There will be two hosts, one for the root domain and another wildcard for all subdomains. If this isn’t ready don’t fret, it will be in 24 hours, and then you can use SSL. There is no rush since you must wait for the nameserver changes to propagate at the registrar anyway. You will see the SSL which covers two hosts via the Universal SSL pictured like so:
6) The last step to set up Cloudflare for your domain is to proceed to optimize your new Cloudflare service using suggestions and information below as desired.
Our Recommendations
We recommend the following when using Cloudflare, and I’ll explain why:
- Try to use Cloudflare nameservers for your domains from the start.
One thing that Cloudflare does well is to hide the main server’s IP; however, there are ways around this, and I’m going to tell you how to avoid some of those. One is to query historical DNS records for the domain, thus finding any old nameservers you used before Cloudflare that may have pointed directly to the server. If you set up the nameservers from the start with Cloudflare instead of any locally-hosted nameservers, you won’t have to worry about this. To set up nameservers with Cloudflare from the start, add the domain to Cloudflare and allow it to scan for the records. It will show the following error:
You can then click the domain in the top left corner of the Cloudflare dashboard to go to the overview. You will see a message stating “Status: Website not active (DNS modification pending) like below:
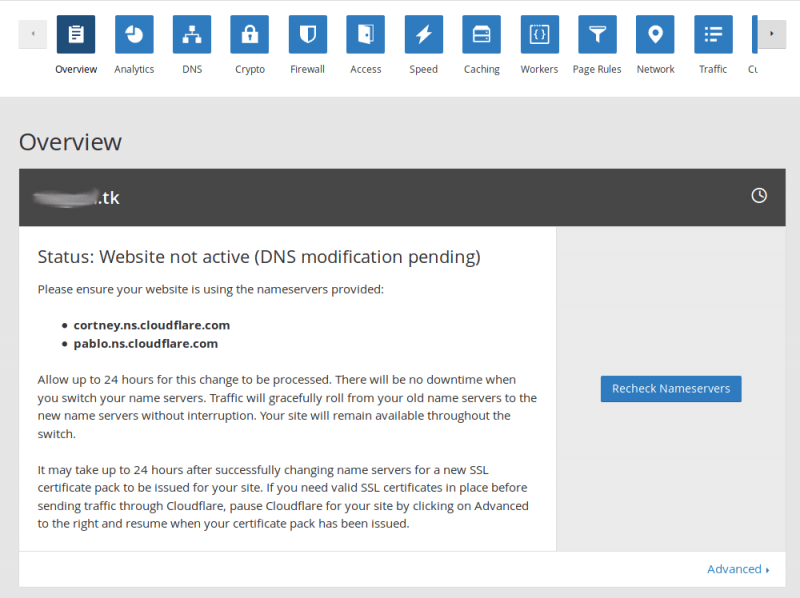
You will see the nameservers for the Cloudflare account here. Go ahead and log into the registrar where the domain is registered and assign these as the custom nameservers for the domain. Now, it won’t be possible to query historical DNS records to find any previous nameservers to find the actual IP of the server hosting the domain.
- Use a remote mail server.
Now, using only Cloudflare nameservers won’t matter if you don’t use a remote mail server, and I’ll show you why. If you refer to the image below, you can see a domain that I’ve set up for this article. You see that its NS records are Cloudflare records first. Then you can see that I’ve queried the MX record, and this gives an odd-looking record. Cloudflare would in the past use a dc-domain.tld record as a ‘direct connect’ record. This ‘dc’ record would give the A record for the server but did little to hide the server’s main IP since anyone can just query the A record for ‘dc-’domain.tld to find it. Thus, they began appending the digits to the ‘dc’ and prepending this as a whole to the domain. The numbers were not so obvious and easy to guess. But, you can query the MX record if the domain is using a local mail server, and this would give the ‘direct connect’ record, and then querying the A record of this would give the server IP (at least the mail server IP).
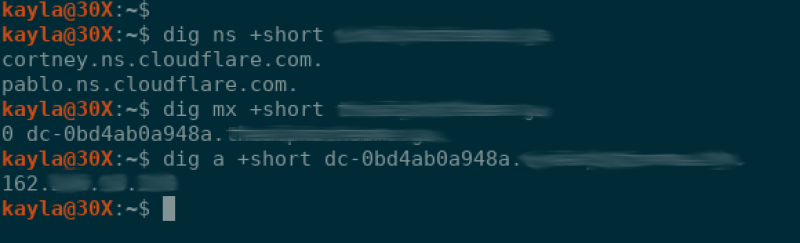
A more compact one-liner to accomplish this would be as follows:
dig a +short $(dig mx +short domain.tld)You would replace domain.tld with the actual domain you want to query. This will give the IP of the mail server, and thus the site’s source server IP (allowing an attacker to bypass security measures put in place by Cloudflare). Thus, it is recommended that you use a remote mail server if the objective is to conceal your server IP. Using a remote mail server such as those provided by Google would be optimal as those records would be returned when the MX record is queried instead.
- Be mindful of any other ‘direct connect’ records you create.
You will want to avoid setting any obvious subdomain A/CNAME direct connect records that can be guessed easily and then queried, too, if at all possible. I mean records such as ‘ftp’, ‘dev’, ‘host’, etc. If subdomains are not ‘grey clouded’ (show an orange cloud next to the record indicating that Cloudflare is enabled for the domain), then Cloudflare will hide the source server IP. If you need a direct connection to the server via the domain, you could set an A record for a random string subdomain, but if you are willing to go this far, you may as well just simply use the IP when you need to connect directly (such as when you need to use FTP, etc).
- Whitelist Cloudflare IP’s in Your Server’s Firewall
A firewall will typically have a connection limit that limits simultaneous connections from a single IP. If all traffic for a busy site, or several sites, is coming from a small set of IPs, then it is easy to see how these IPs can exceed this limit and become blocked if these IP’s are not whitelisted, Cloudflare may become blocked in your server’s firewall and this could cause downtime for your sites! Thus, it is important to be sure to whitelist Cloudflare IP’s, which can be accomplished using the following lists of IPs:
This type of blocking will look like this, but the IPs will all belong to Cloudflare, which will be U.S. IPs rather than Indian IPs, and the log entry may even display the rDNS of the IP blocked, which will sometimes explicitly state that it belongs to Cloudflare:
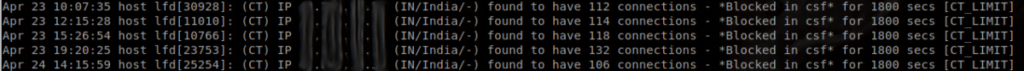
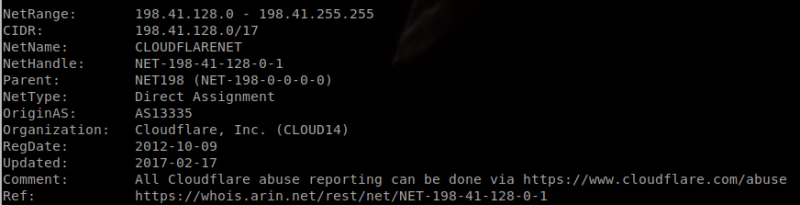
You could do the following to find out if these IPs are in fact Cloudflare’s:
whois [IP]*You must replace [IP] with the actual IP. Here is what the first section of the output will look like, which is enough to tell us that this IP is Cloudflare’s:
To whitelist these IPs on a cPanel server via CSF/LFD, you could use the following command:
curl https://www.cloudflare.com/ips-v6 | while read E; do echo "$E # CloudFlare" >> /etc/csf/csf.allow; done && curl https://www.cloudflare.com/ips-v6 | while read E; do echo "$E # CloudFlare" >> /etc/csf/csf.ignore; done && curl https://www.cloudflare.com/ips-v4 | while read E; do echo "$E # CloudFlare" >> /etc/csf/csf.allow; done && curl https://www.cloudflare.com/ips-v4 | while read E; do echo "$E # CloudFlare" >> /etc/csf/csf.ignore; done && csf -raHere is the output of running this command on my system:
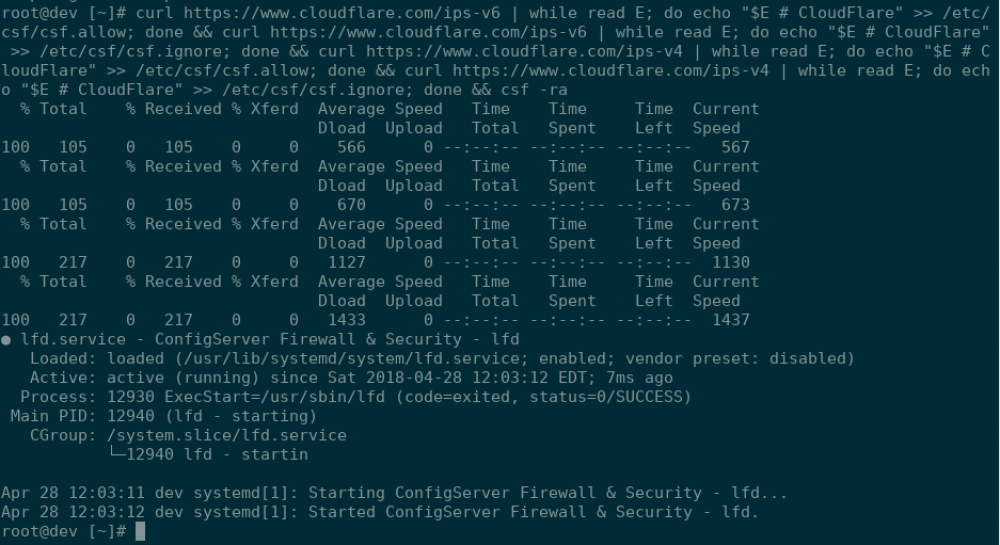
You can confirm that the IPs have been added to the appropriate files with the following command:
grep CloudFlare /etc/csf/csf.allow /etc/csf/csf.ignore You should see output similar to this:
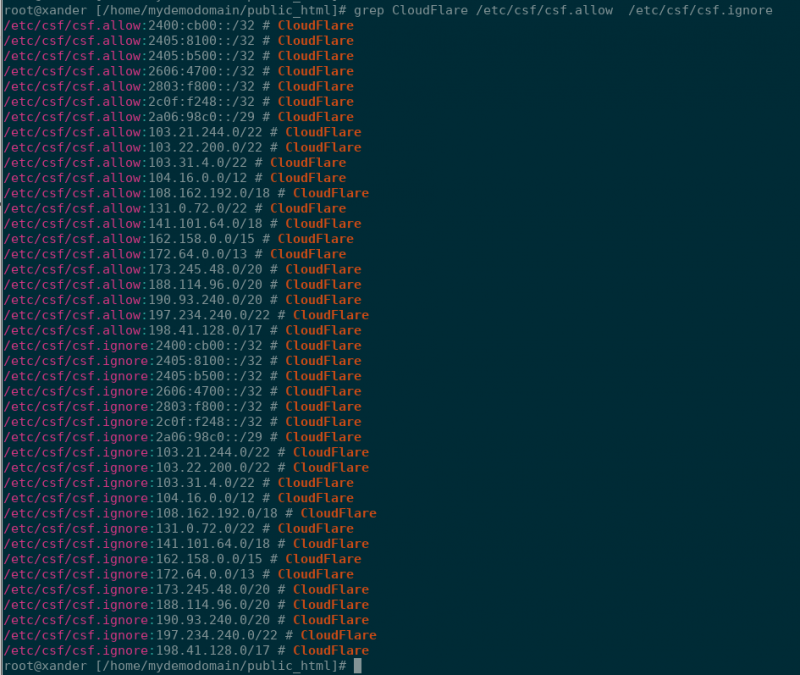
The only issue I see with adding these to csf.allow and csf.ignore (whitelisting via CSF/LFD firewall that is used at Knownhost) is Cpanel/WHM/Webmail brute forcing via a domain hosted on Cloudflare.
For instance, an attacker would be able to brute force the following repeatedly without ever getting banned by CSF/LFD:
mydomain.tld/cpanel
Unfortunately, there is no solution for this at this time. There is a lot of speculation about how this could be resolved, however, none have been agreed upon as viable solutions without their own problems. There have been many posts discussing this, though, and a few are linked below for you to reference that explore the possibilities via cPHulk.
Page rules and/or Rate Limiting could possibly be used to help circumvent this issue (the first 10,000 requests and blocked requests are free, and the cost is $0.05 per 10,000 legitimate (non-blocked) requests thereafter.), but hopefully, Cloudflare and cPanel can come together to find a definite solution for this. Configuring Cloudflare Rate Limiting Introducing Page Rules: Fine Grained Control over CloudFlare’s Features
- Allow the IPs of the services you use to access your website
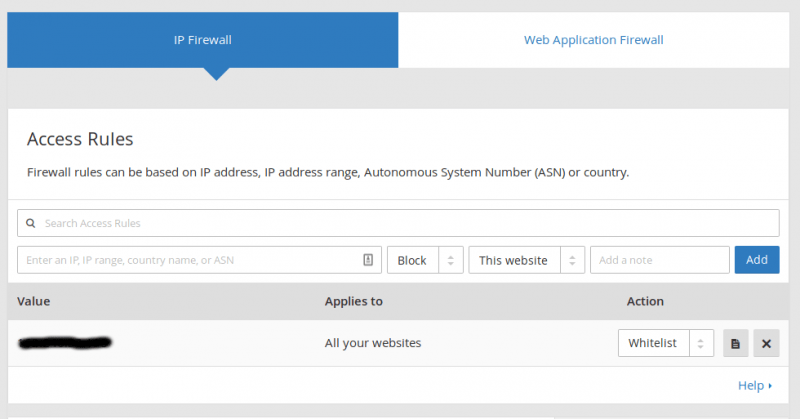
If you use certain APIs, certain payment gateways (Stripe, PayPal, etc), or other services that connect to your sites frequently, you should whitelist them in the IP Firewall. Log into your Cloudflare dashboard, click the Firewall tab, and look for the following to add the IPs of these services:
- Install Mod_Cloudflare to restore the actual visitor IP addresses in your Apache logs.
If you do not, all requests will be shown as originating from Cloudflare IP addresses, which can make it impossible to track/block abusive traffic via the domain access logs manually. Thus, it is imperative that this is done. Knownhost will gladly install this module for you if you find it is not already installed. To check whether this module is installed, you can use the following commands:
httpd -M | grep -i cloudflareOR
rpm -qa | grep -i cloudflareIf the module is installed, you will see output like shown in the image below:
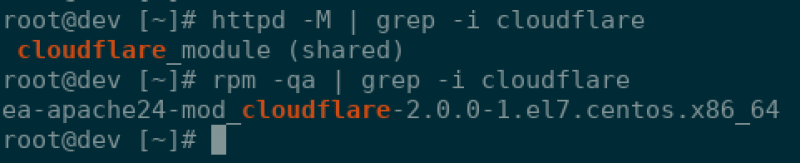
Mod_Cloudflare can be installed as ‘root’ via SSH using the following command for CentOS7/EasyApache4 cPanel servers:
yum install ea-apache24-mod_cloudflare.x86_64If you are running an older server, you may need to do this first:
cd /etc/yum.repos.d/
wget http://download.opensuse.org/repositories/home:Jperkster:EA4_Mod_Cloudflare/CentOS-7/home:Jperkster:EA4_Mod_Cloudflare.repoNow, confirm the installation was successful by using the same commands you used to check to see if the module was installed previously.
- Consider utilizing Cloudflare’s Rate Limiting to thwart DDoS and brute force attacks.
The only issue is this service is * not free * but is billed according to usage. When you click Enable in your Cloudflare dashboard under Firewall tab, you will see the following:
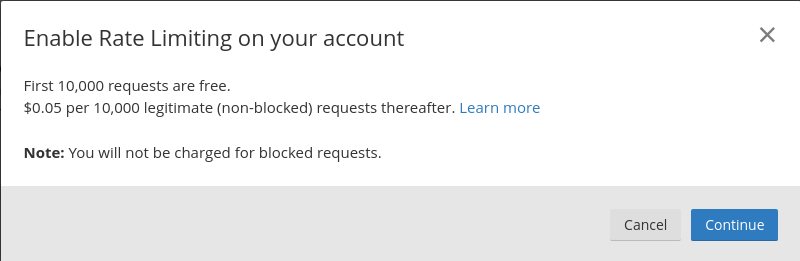
It will ask you for billing information, and then you proceed to add your custom rules. Here are more details about adding the rules:
support.cloudflare.com/hc/en-us/articles/115001635128
- Consider Using Page Rules to Exclude Your Site’s Admin Section From Cloudflare
You may want to do this if caching, minification, and other Cloudflare performance features have the potential to break your site’s backend. Try this if your website appears broken or parts of it are missing after enabling Cloudflare.
Cloudflare has some excellent tutorials for Page Rules here
How to Optimize Your Domain With Page Rules
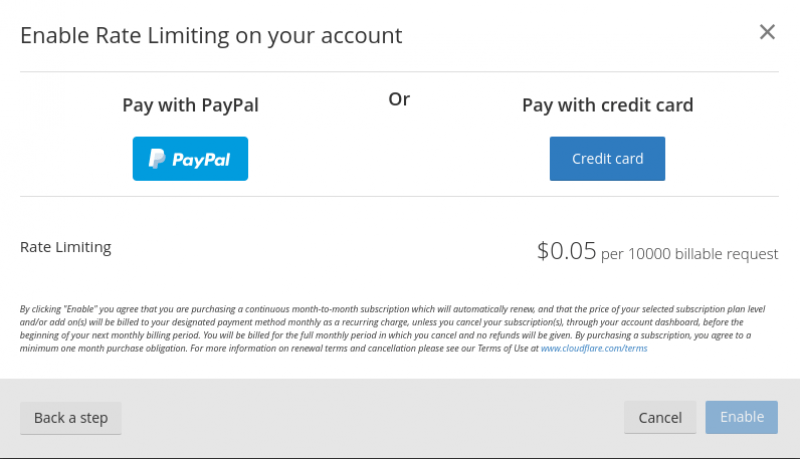
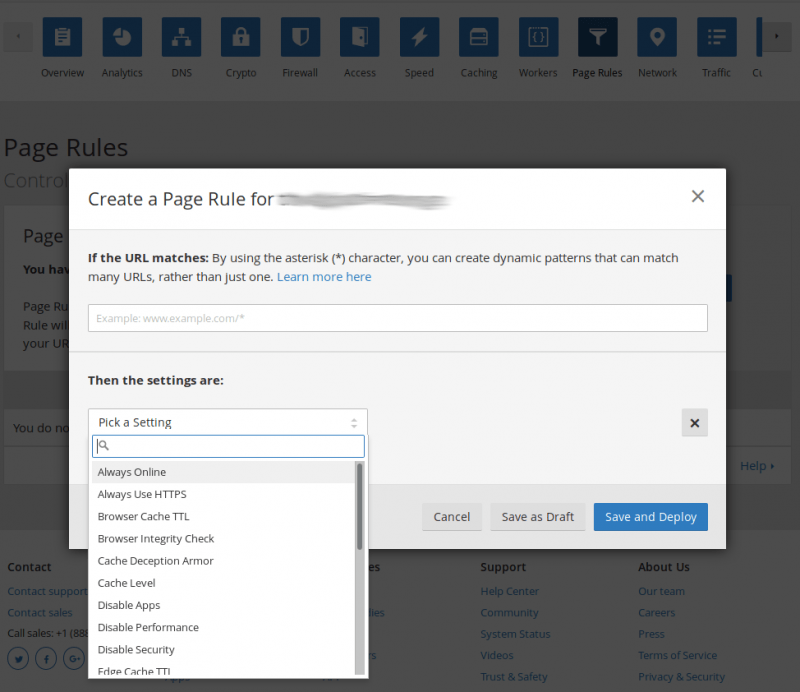
You get 3three page rules with the free account and these can be found in the Cloudflare dashboard under the Page Rules tab:
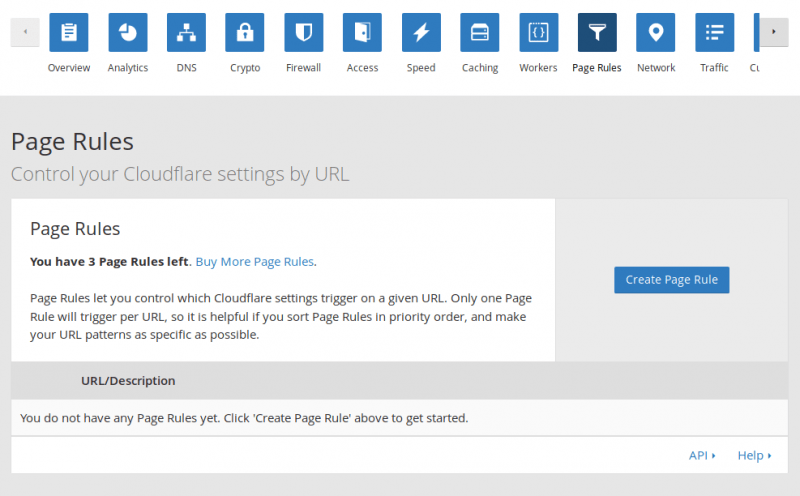
Creating page rules is quite easy with the intuitive interface:
Taking Full Advantage of Cloudflare’s Free Plan
Now, to get the most out of the Cloudflare free account, check these options out:
Under the Speed Tab:
- Enable Auto Minify
This will minify HTML, CSS, and JavaScript and supports dynamic pages, too!
If you want to test some beta features under this tab:
- Enable AMP (BETA)
Thanks to AMP technology, AMP-enabled pages load 3-5X faster than normal mobile pages. Remember that this is BETA at the time of writing this article, so this could change to a paid feature in the future.
- Enable Asynchronous Javascript Loading Rocket Loader (BETA)
This is also BETA at the time of writing this article, and pricing for this feature is subject to change. Get more information about how this feature improves the load times of your external resources here. How CloudFlare Rocket Loader Redefines the Modern CDN
The article states that Rocket Loader does a bunch of things:
- It ensures that all the scripts on your page will not block the content of your page from loading;
- Loads all the scripts on your page, including third-party scripts, asynchronously;
- Bundles all the script requests into a single request over which multiple responses can be streamed;
- Uses LocalStorage on most browsers and nearly all smartphones to more intelligently store scripts so they aren’t refetched unless necessary.
How CloudFlare Rocket Loader Redefines the Modern CDN
Under the Caching Tab:
- Adjust Browser Cache Expiration accordingly for your needs (set to 4 hours by default)
Under the Apps Tab:
- Sign up for Cloudflare Apps notifications! Receive email notifications when new apps or features are available!
Under the Scape Shield Tab:
- Enable Hotlink Protection to protect your images!
Luckily, you don’t really need to worry about your bandwidth here thanks to Cloudflare having no limit on bandwidth (as long as you comply with their terms of service), however, if you don’t want your images used on other sites, you’ll want to enable this option.
Under the Crypto Tab:
- Make sure to use full crypto.
Important: We recommend that you use Cloudflare’s Origin Certificate for this. Why? For ease of issuance and renewal. If you were to use AutoSSL (which is amazing under most circumstances), it would check the domain’s IP during automated renewal, find that the IP is external to the server (Cloudflare’s IP), and then fail to renew due to this. To use AutoSSL with Cloudflare, you would have to manually disable Cloudflare every 3 months long enough to initiate the AutoSSL renewal process and allow it to complete domain validation (which is warned to take up to 2 days). To avoid this inconvenience, just use Cloudflare’s origin SSL instead! They have already confirmed you own the zone for the domain, so there no need to repeat the domain validation process again. The CSR can be generated in your Cloudflare account, and the SSL then issued for 15 years! This eliminates the need to generate the CSR at the server and the headache that comes with frequent renewals. You just need to install the SSL certificate on the server. Do note, though, that the SSL will throw errors if Cloudflare is disabled since it is only recognized by Cloudflare (this is no problem when Cloudflare is enabled as all traffic is routed via Cloudflare). Another benefit of the Cloudflare Origin SSL is that it is an optimized SSL, meaning that it is small and fast to transmit. Knownhost will gladly install the SSL at the server for you once you retrieve it. Just remember that you must log back into your Cloudflare account once installed and change your crypto settings to Strict. Note, also, you have the option of using a self-signed SSL to set up Full Crypto. However, it won’t be valid for as long as Cloudflare’s Origin Certificate, and it will cause the site to display SSL warnings in the browser. Overall, the Cloudflare Origin SSL seems like the best option in regards to optimization and effort to maintain.
- Enable Always Use HTTPS
– This will prevent mixed content errors! Mixed Content Errors are those errors that occur with sites that have a valid SSL installed, but the site code links to external resources (Javascript, CSS, images, etc.) via the insecure HTTP protocol instead of HTTPS. These sites often have a green padlock in the browser, with a yellow warning symbol over it, or a warning stating that the site is not ‘fully’ secure. See below:
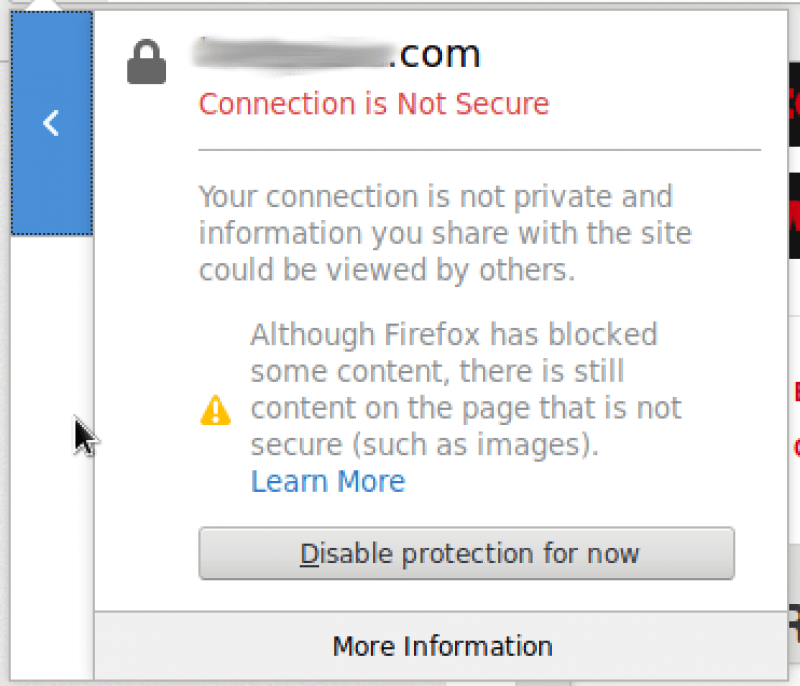
You will likely only see a warning symbol and will need to click it or use developer tools (the security tab) to find more information regarding the error with the SSL, but it is nearly always Mixed Content when this warning is displayed.
When enabling this option at Cloudflare, make sure resource is available via https, and if not, then you may want to consider using either a different resource or different scripts that are more security aware/up-to-date.
The following options are not suitable for all, however, check these settings if you want increased security:
Under the Crypto Tab:
- HSTS *
This requires additional configuration via visiting each browsers’ preload submission URL manually to be most effective and bypass attacks to bypass HSTS.
Note the following quote from Cloudflare: “HSTS is a header that tells browsers that your site is available over HTTPS and will be for a set period of time. Once a browser sees an HSTS header for a site, it will automatically fetch the HTTPS version of HTTP pages without needing to follow redirects. HSTS can be enabled in the crypto app right under the Always Use HTTPS toggle.”
Also, see the following on this subject.
- Authenticated Origin Pulls
This requires additional configuration at the server, but, when enabled, will confirm that all client requests are being routed through Cloudflare and not allowing potential attackers to bypass Cloudflare so that they avoid the Cloudflare security protocols, restrictions, and firewall. In the same way that a client can check a site’s SSL to confirm the server that the site is loading from, an SSL can be installed and used to confirm that the client the server is communicating with is Cloudflare. You don’t want to allow clients to bypass the protections afforded to you by Cloudflare, and this can certainly help with that! An alternative would be to block all access except Cloudflare IPs. One problem with this setup is in regards to gray clouded domains:
Please note that once Authenticated Origin Pulls are enforced by your origin server, any HTTPS requests outside of Cloudflare to your origin will fail including those to gray clouded records on Cloudflare.
Another would be that of troubleshooting. One could not simply disable Cloudflare on the domain and then proceed to troubleshoot the site. Troubleshooting would have to be done through Cloudflare, so you would have to disable caching, empty the existing cache, etc to troubleshoot changes or errors with a site.
- Require Modern TLS
This is rather self-explanatory. Older versions of SSL and TLS are vulnerable to certain attacks, such as “BEAST” and “POODLE”, so this is certainly an option you’ll want to consider.
Under the DNS Tab:
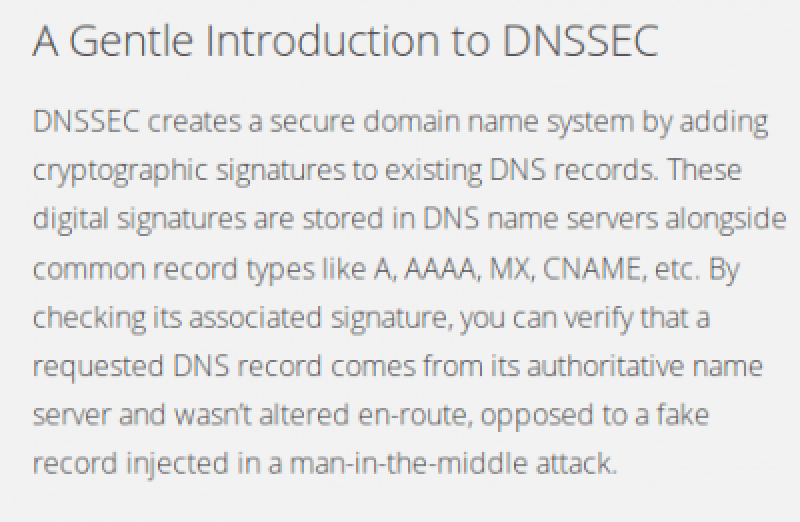
- Enable DNSSEC
The image below is taken directly from the following link since Cloudflare does such a good job of describing DNSSEC.
Other Awesome Features From Cloudflare
Cloudflare even offers a cPanel plugin, which would both be awesome for resellers to offer their clients. Here is a link containing more information (namely installation and configuration instructions):
cPanel Installation Guide
Note: The Cloudflare cPanel plugin has been deprecated and is no longer actively maintained.
We’ll explore Cloudflare for Resellers in an upcoming article.
There are also amazing CMS-specific plugins for Cloudflare, too, which let you manage Cloudflare for that domain via your CMS dashboard (How cool is that!).
Introducing the CloudFlare Joomla Extension
Cloudflare Magento Extension for Performance and Security
More information on the CMS integrations and many more can be found here:
Cloudflare Integration Resources
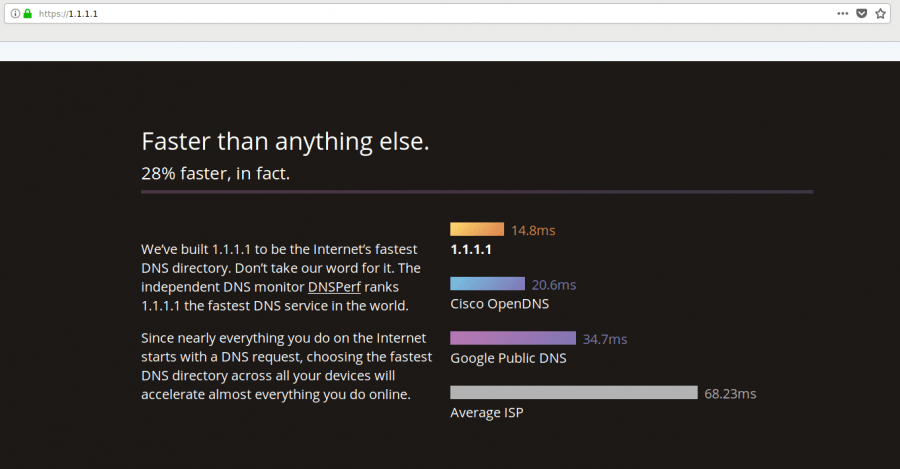
Cloudflare now even offers resolvers as of April 1st (they chose to introduce it on April Fool’s Day because of the ‘4’ and the ‘1’ in the date to represent the 4 ‘1’s of the resolver)!
These are proclaimed to be the fastest resolvers of all (image taken from 1.1.1.1/ ):
You can change your resolvers in WHM using the following instructions:
You will see the following:
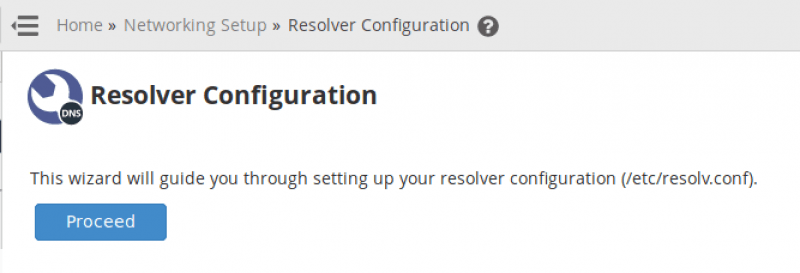
Click “Proceed”
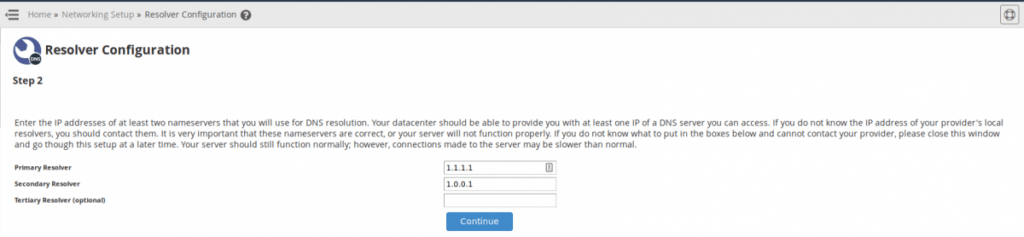
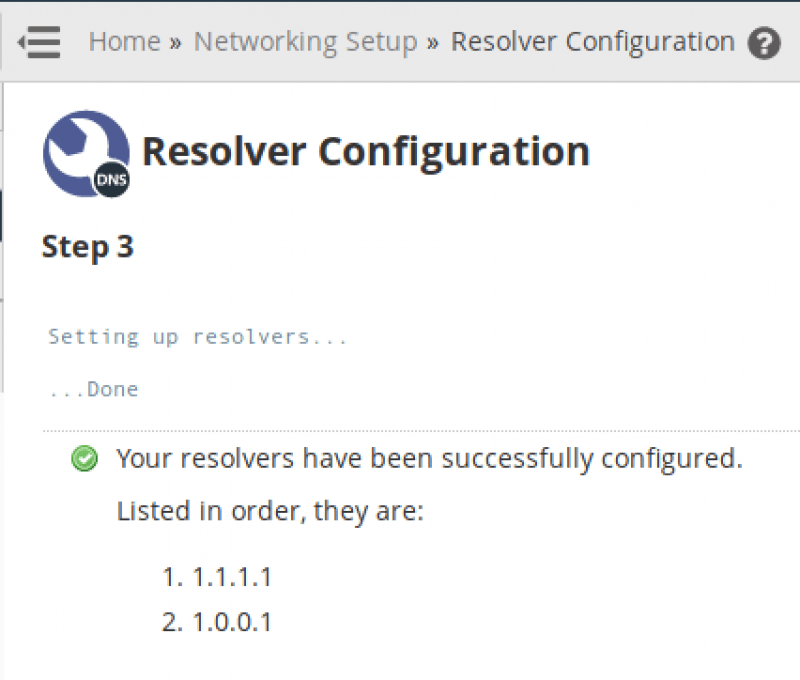
Click “Continue”. You will see the following confirmation that this is complete:
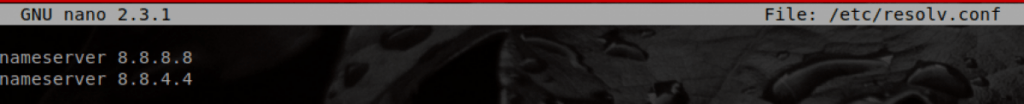
Or simply log into your server via SSH as the root user, and run the following to edit the file:
nano /etc/resolv.confHere is what the file looks like on my server using Google resolvers:
Here is what the file looks like after the edits to use Cloudflare resolvers:
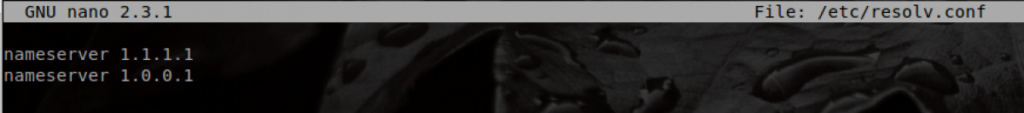
Ctrl X + y + Enter to save the changes when editing with Nano. You should now see a 28% increase in the speed of your resolvers (according to 1.1.1.1/)!
Note that you can even configure an IPv6 Resolver if you have IPv6 enabled on your server.
Cloudflare is evolving and innovating daily and definitely worth the effort to configure. As always, if you have any questions about the configuring anything in the server to work with Cloudflare, Knownhost is here to help!